Multi-cloud strategies are frequently positioned as a structural response to vendor lock-in. The underlying assumption is straightforward: if workloads are distributed across multiple providers, dependency risk is reduced. Diversification appears to increase resilience.1
Yet diversification is not equivalent to substitutability. Optionality is not defined by how many providers appear on an architectural diagram — it is defined by whether a capability can be replaced without systemic redesign. Distributing workloads may reduce concentration risk, but it does not automatically dissolve structural entanglement, especially where integration layers and proprietary service dependencies are concerned. Research into cloud vendor lock-in shows that interoperability and portability challenges remain core structural inhibitors to change.2
Optionality is therefore not a procurement outcome. It is an architectural property.
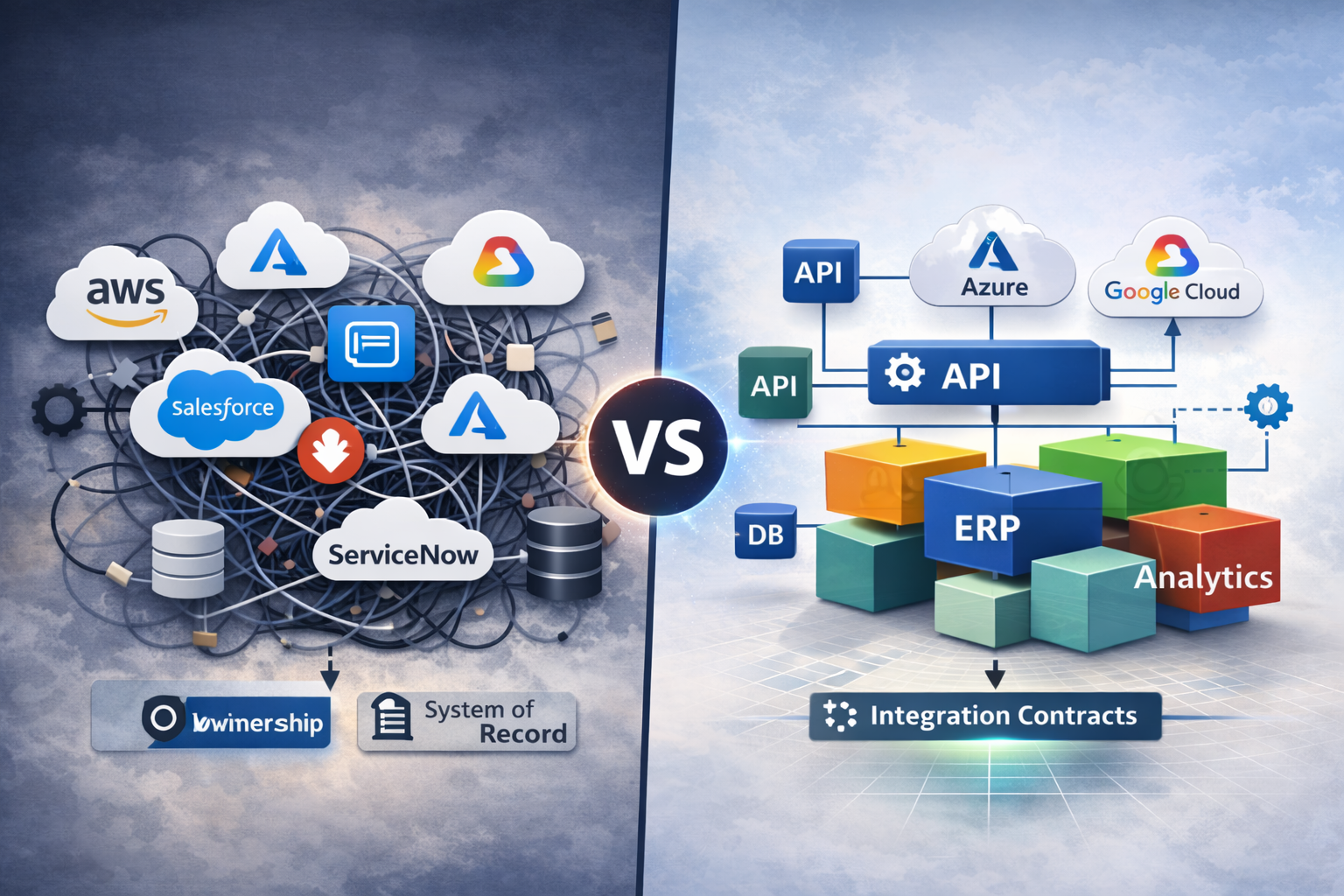
1. Distribution Is Not Substitutability
A multi-cloud landscape often reflects deliberate risk diversification. Infrastructure may run across hyperscalers. SaaS platforms may be sourced from different vendors. Regulatory exposure may be distributed geographically.
However, substitutability requires more than distribution. If replacing a CRM platform forces changes in downstream analytics, identity management, billing integration, and workflow orchestration, the dependency surface extends beyond the system itself. The replacement cost is not limited to license migration — it propagates through process logic, data contracts, and operational routines. Research confirms that lock-in persists precisely because proprietary technology, contract terms, and network effects can make switching prohibitively complex.3
Architectural dependency is measured by ripple effects. Where ripple effects are large, optionality is low — regardless of how many cloud providers are involved.
2. Modularity as the Precondition for Optionality

Strategic optionality emerges from modular design. Modularity is not an aesthetic preference — it is a structural precondition for substitutability. Studies of cloud architecture highlight that standardised APIs and vendor-agnostic services are essential to mitigate lock-in.4
Business Capability Modularity
Capabilities must be clearly bounded. Ownership must be explicit. System-of-record responsibility must be unambiguous.
When multiple platforms co-own a business process without clear domain boundaries, replacing one system requires redistributing responsibility across the landscape. That redistribution is rarely neutral — it affects reporting logic, integration semantics, and operational workflows.
Clear capability boundaries reduce the blast radius of change.
Technical Modularity
Technical modularity manifests in stable integration contracts and controlled coupling.
Indicators include:
- APIs that represent durable capability interfaces rather than convenience endpoints
- Data models that are not implicitly shared across domains
- Clear separation between core application logic and integration logic
- Limited reliance on proprietary execution environments for critical business functionality
Where vendor-specific services become embedded into core process logic — for example through proprietary workflow engines or event buses — substitutability decreases.
Modularity is revealed in the ability to change implementation without redefining responsibility.
3. The Integration Layer as Architectural Diagnostic
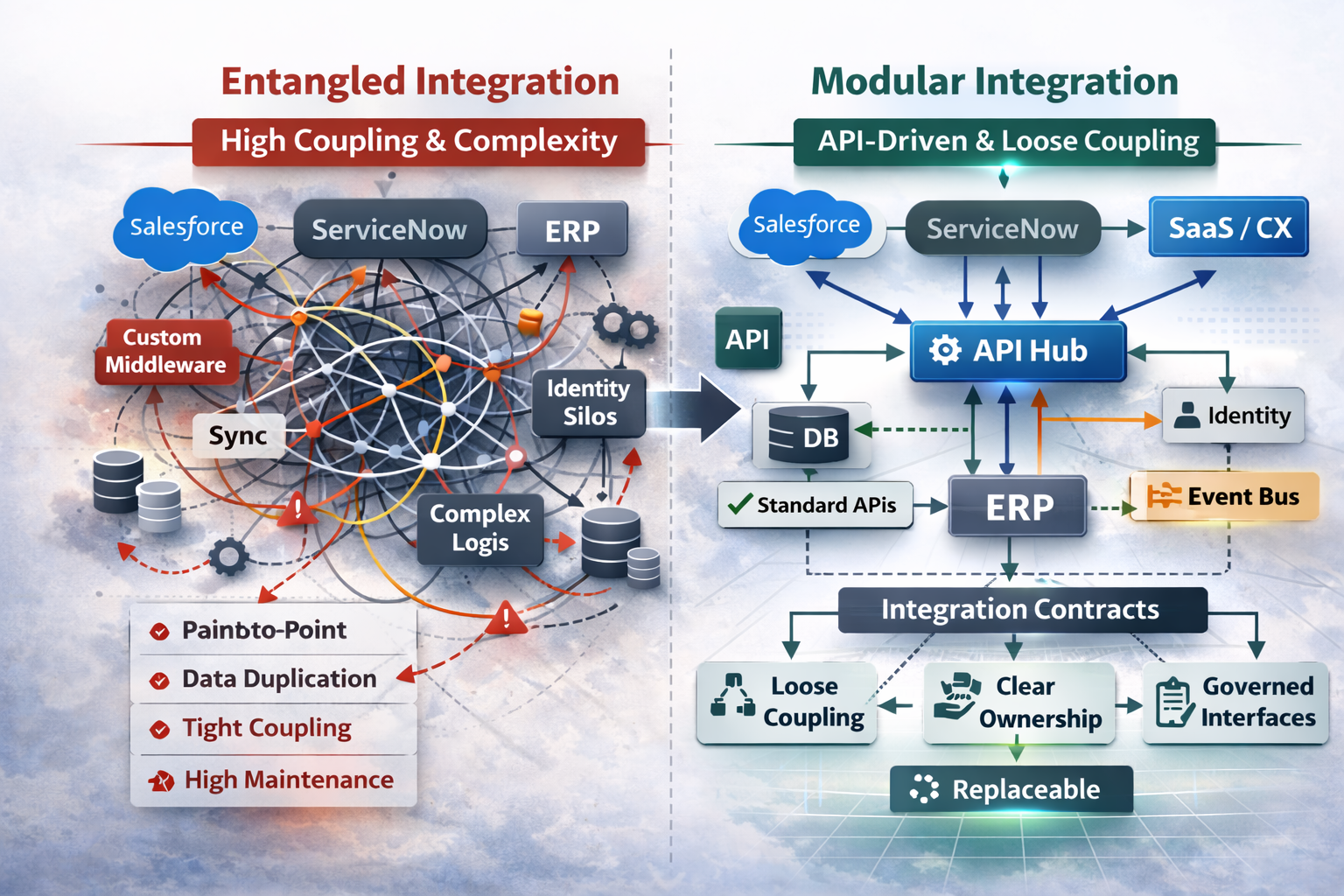
The integration layer is often treated as plumbing. In reality, it is the most reliable diagnostic surface for structural dependency.
Systems that integrate through robust, consistent, versioned APIs typically produce flatter integration architectures:
- Fewer transformation layers
- Reduced orchestration complexity
- Limited custom middleware
- Clear data ownership boundaries
In contrast, landscapes with continuous object synchronization, transformation-heavy middleware, and cross-platform identity entanglement accumulate architectural gravity. As noted in integration research, heterogeneity without disciplined modularity increases complexity and cost.5
Integration complexity increases monitoring overhead. Monitoring overhead increases operational exposure. Operational exposure increases risk and cost.
Thus, the shape of the integration architecture reflects the depth of entanglement more accurately than any vendor strategy document.
4. When Multi-Cloud Increases Structural Dependency
Without modular discipline, multi-cloud may amplify complexity rather than reduce risk. According to one multi-cloud analysis, while multi-cloud can enhance architectural resilience, it also introduces operational challenges, security risks, higher costs, and integration difficulties when not supported by orchestration discipline and standardisation.6
Each additional provider introduces:
- A distinct identity and access model
- A distinct observability stack
- A distinct compliance interpretation
- A distinct release cadence
- A distinct operational failure mode
If integration patterns are not simplified through clear contracts, complexity compounds.
In such environments, outages are rarely isolated. They cascade through integration paths. Operational teams spend more time stabilising interfaces than evolving capabilities.
What was intended as diversification becomes fragmentation.
5. Optionality as Governance Discipline
True optionality requires deliberate architectural governance. Cloud adoption frameworks emphasise this: strategic planning, dependency audits, and cloud-agnostic design patterns are key to avoiding long-term lock-in and preserving strategic flexibility.7
This includes:
- Explicit capability mapping and system-of-record designation
- Defined integration contracts treated as long-term architectural boundaries
- Controlled use of proprietary platform services in core business logic
- Periodic substitution scenario modelling
- Evaluation of blast radius before deep platform adoption
Optionality does not imply constant migration readiness. It implies conscious dependency acceptance.
Architectural governance makes dependencies visible. Visibility enables decision-making. Decision-making preserves manoeuvrability.
Optionality is sustained through clarity.
Conclusion
Multi-cloud distributes vendors.
Modularity distributes risk.
Strategic optionality is not achieved by increasing the number of providers in the landscape. It emerges when architectural boundaries allow capabilities to evolve, be replaced, or be reallocated without destabilising the enterprise.
The decisive question is not how many clouds are in use.
It is whether the architecture can absorb change without systemic redesign.
Optionality is not a topology.
It is a structural condition.
References
-
Munnangi, V. K. R. (2025). Multi-Cloud and Hybrid Cloud Strategies for Enterprise API Architectures. Journal of Computer Science and Technology Studies. ↩︎
-
Opara-Martins, J. S., Sahandi, R., & Tian, F. (2016). Critical analysis of vendor lock-in and its impact on cloud computing migration: A business perspective. Journal of Cloud Computing. ↩︎
-
“Vendor lock-in”, Wikipedia (2026). ↩︎
-
“Multicloud”, Wikipedia (2025). ↩︎
-
Integration research (2025). Integration von Unternehmensprozessen. ↩︎
-
Promethium Guide (2025). Multi-Cloud Data Strategy: Avoiding Vendor Lock-In. ↩︎
-
Cloud adoption governance frameworks (various sources). ↩︎